Picus
Picus is a leading cybersecurity validation company that helps organizations continuously test and measure the effectiveness of their security controls. Through Breach and Attack Simulation (BAS) and exposure validation, Picus enables security teams to identify gaps, reduce risk, and strengthen defenses before real attackers can exploit them.
The Picus Security Validation Platform
See Your Security Through an Attacker’s Eyes
The Picus Security Validation Platform continuously emulates real-world attack techniques across your environment to validate whether existing security controls can actually stop them. It provides actionable insights to improve detection, prevention, and response capabilities.
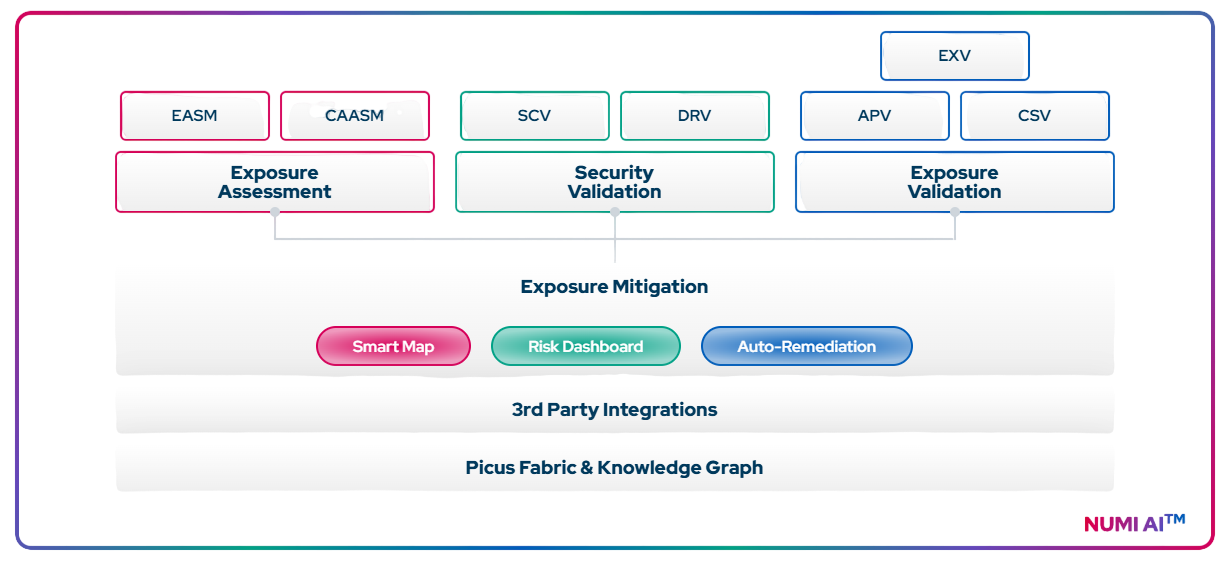
Core Capabilities
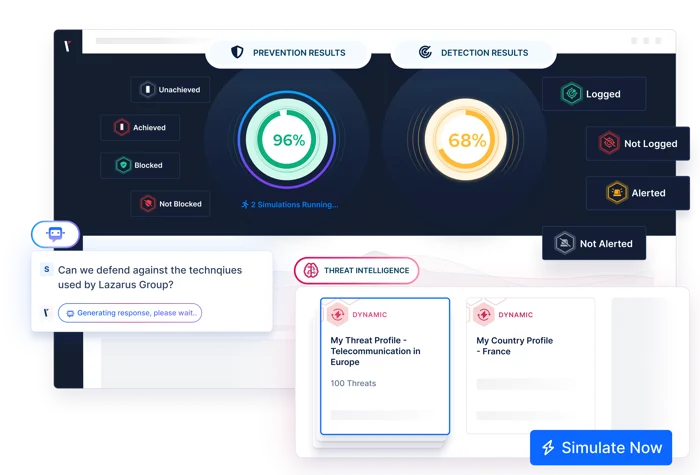
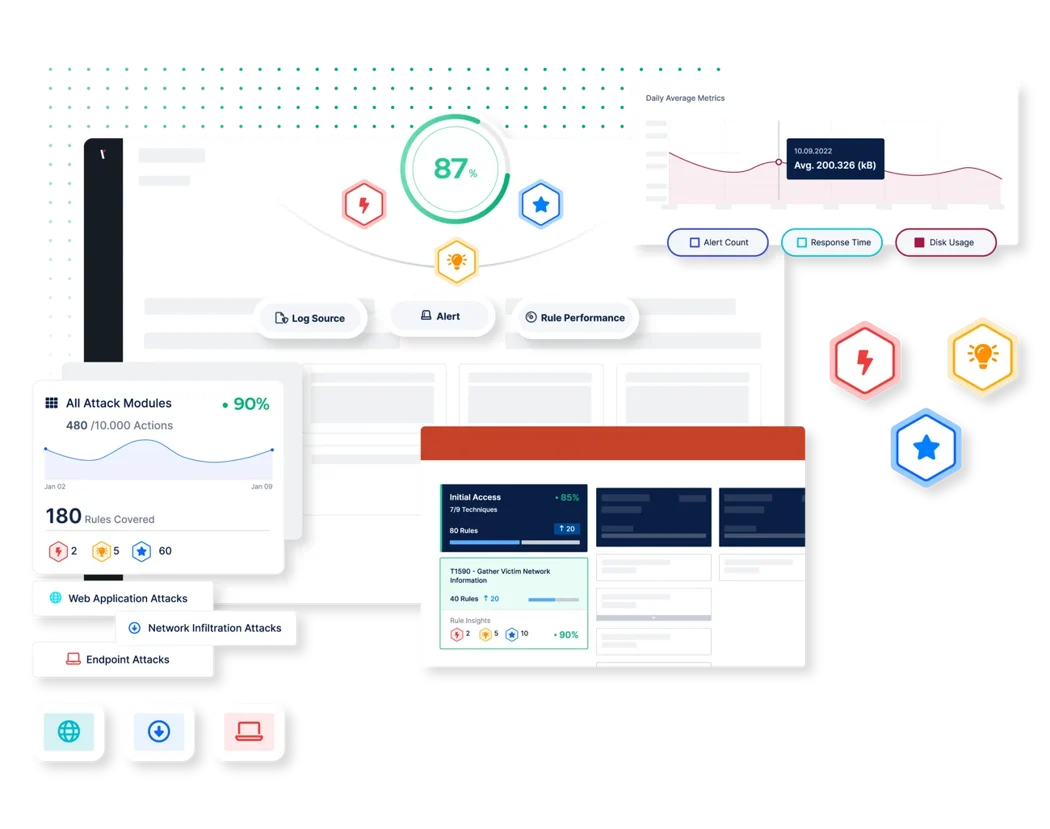
Breach and Attack Simulation (BAS)
Continuously emulate real-world attack techniques across endpoints, networks, and cloud environments to test defensive effectiveness.
- Simulates real adversary tactics, techniques, and procedures (TTPs) mapped to MITRE ATT&CK
- Runs safe, automated attack scenarios including ransomware, malware, and lateral movement paths
- Validates prevention and detection controls under real attack conditions
- Identifies security gaps before attackers can exploit them
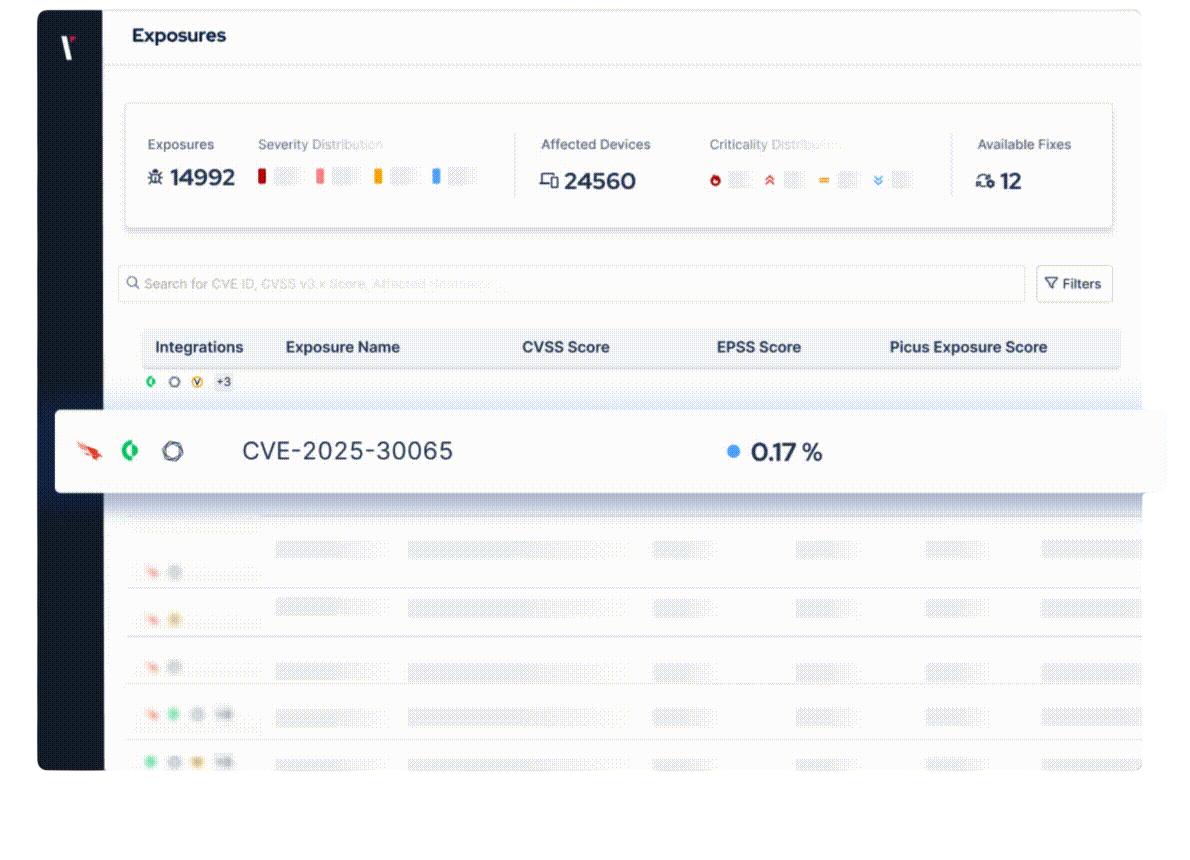
Exposure Validation
Identify and validate which vulnerabilities and misconfigurations are truly exploitable in your environment.
- Tests real exploitability instead of theoretical risk scoring
- Prioritizes exposures based on actual attack success probability
- Reduces alert fatigue by focusing only on actionable risks
- Helps security teams understand real-world risk impact
Security Control Validation
Continuously test the effectiveness of security tools and configurations across your environment.
- Validates performance of EDR, SIEM, firewalls, email security, and endpoint controls
- Identifies misconfigurations and detection blind spots
- Measures control coverage against active threat techniques
- Ensures security investments are delivering expected protection

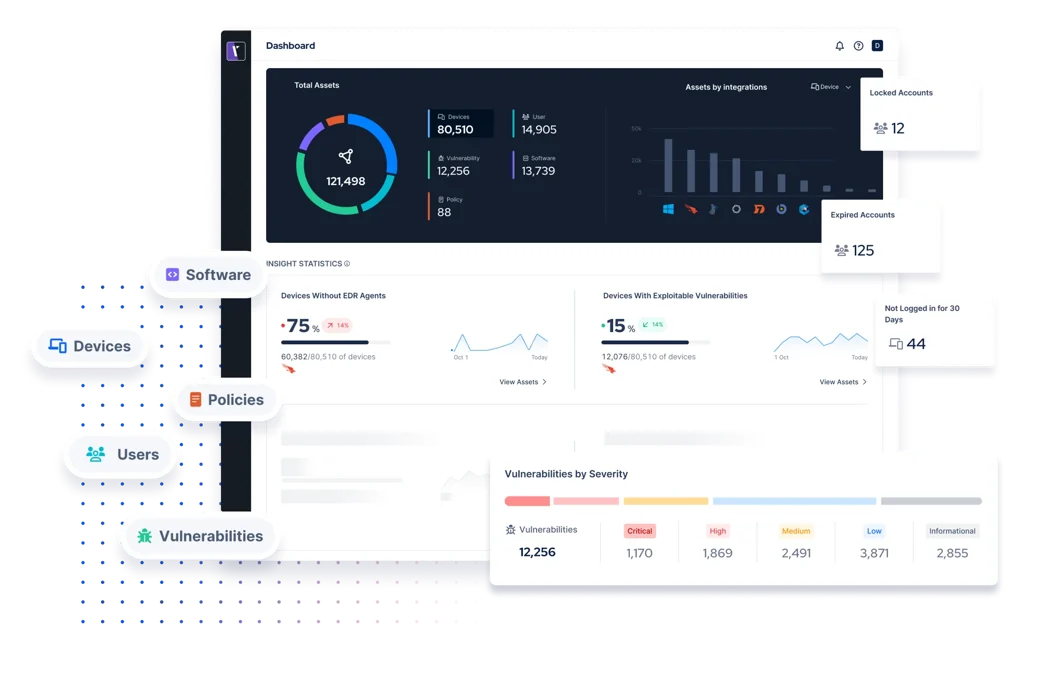
Attack Surface Validation
Gain continuous visibility into how exposed your environment is to potential attackers.
- Maps exposed assets, vulnerabilities, and misconfigurations
- Identifies attack paths across hybrid infrastructure
- Highlights weak entry points across internal and external environments
- Helps reduce unnecessary exposure across the attack surface
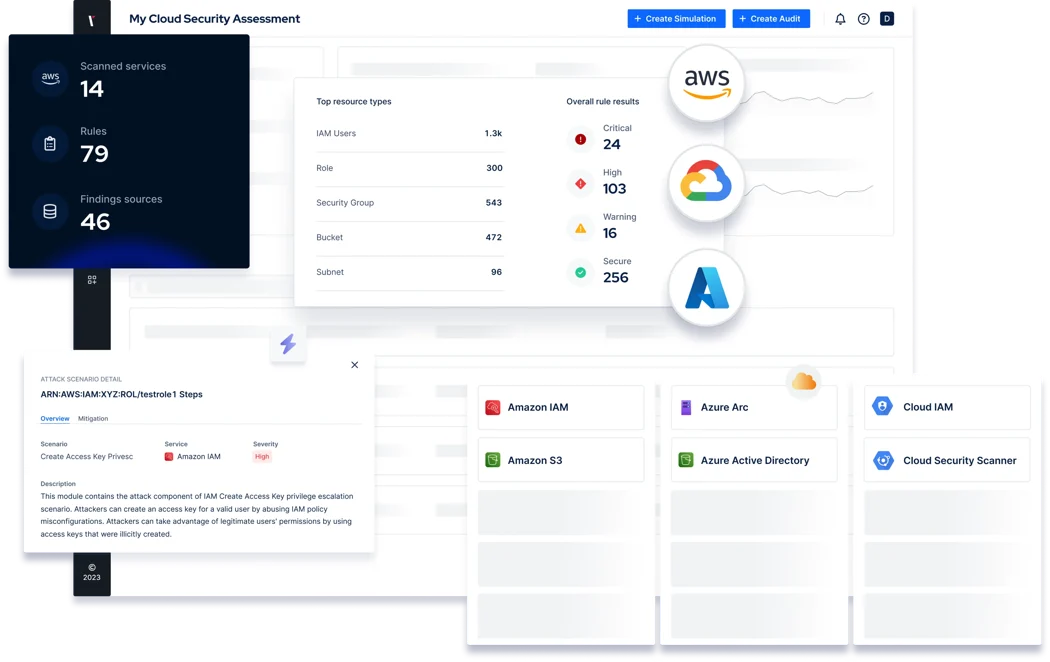
Cloud Security Validation
Continuously validate security posture across cloud and hybrid environments.
- Simulates cloud-native attack scenarios across AWS, Azure, and GCP
- Detects misconfigurations and identity-based attack paths
- Validates cloud security controls and configurations
- Improves resilience in multi-cloud environments
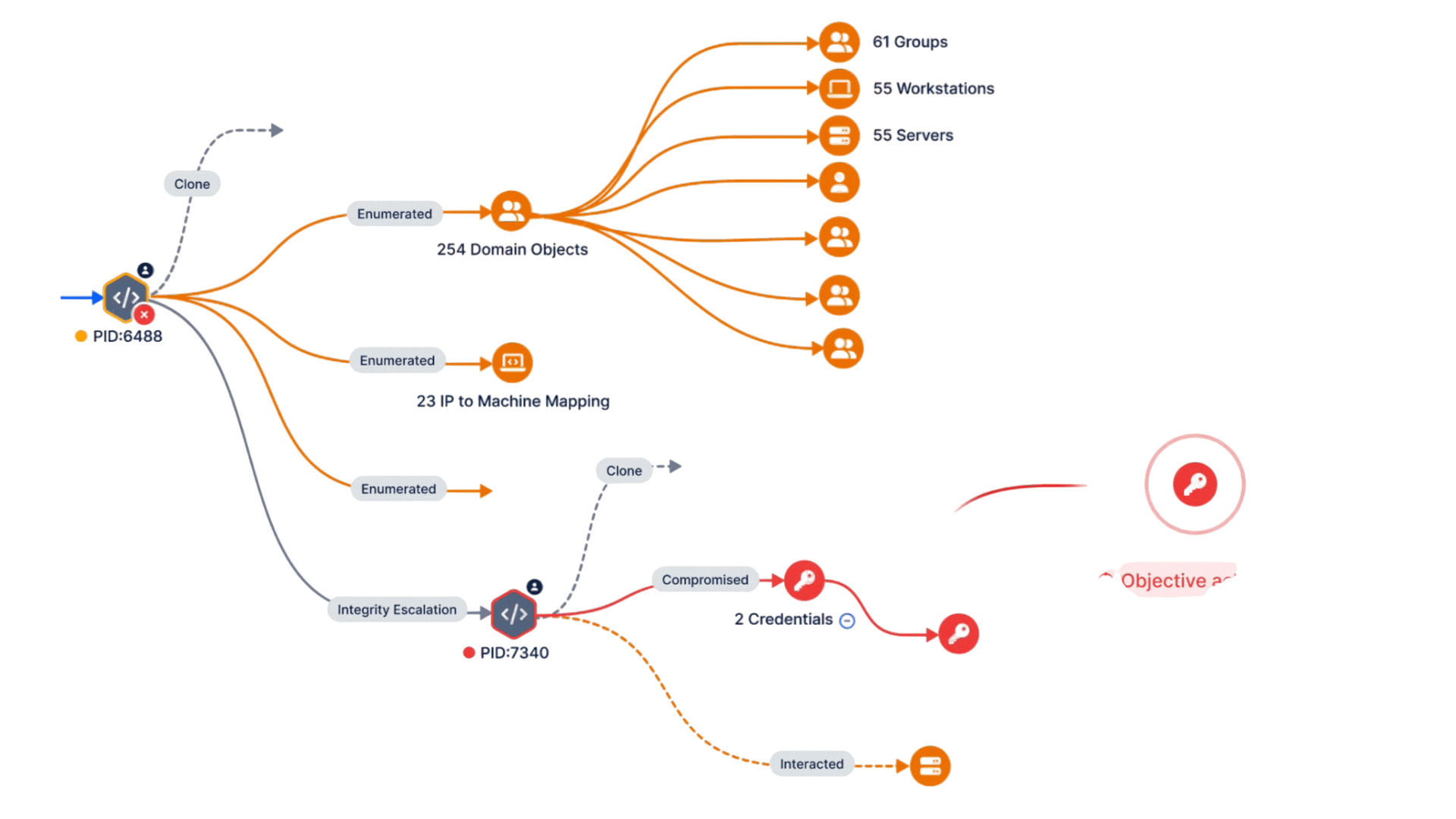
Attack Path Validation
Understand how attackers could move laterally within your environment.
- Simulates real-world attack chains from initial access to critical assets
- Identifies privilege escalation and lateral movement opportunities
- Maps multi-step attack paths across hybrid infrastructure
- Helps prioritize remediation based on real attack feasibility
Detection Rule Validation
Continuously test SOC detection capabilities against real attack scenarios.
- Validates SIEM detection rules and SOC alert coverage
- Identifies blind spots in detection logic
- Measures effectiveness of existing detection engineering
- Improves SOC response accuracy and visibility
Why Picus?

Real Attack Simulation, Not Theoretical Testing
Validates security controls using real-world attack scenarios

Continuous Validation Approach
Security is tested daily, not annually or quarterly

Risk-Based Prioritization
Focus on exposures that attackers can actually exploit

Vendor-Agnostic Coverage
Works across existing security stack without replacement

Action-Oriented Insights
Clear remediation steps to improve defenses quickly

MITRE ATT&CK Alignment
Full visibility into coverage across attacker techniques
Validate your Security Controls with The Picus Complete Security Control Validation Platform
Become Proactive in your Security Operations with Threat-Centric Security Control Validation.
Leverage the Picus Complete Security Control Validation Platform to get 360° visibility of your cyber defenses. Test your defenses against the latest threats. Fully automated. Easy to use. Customizable.